Enterprise
Security Management
AxiomV Enterprise Security Management System for large multi-site/multi-tenant applications, seamlessly integrates Access Control, Alarm Monitoring, and Video Surveillance into an elegant and versatile building management and security system

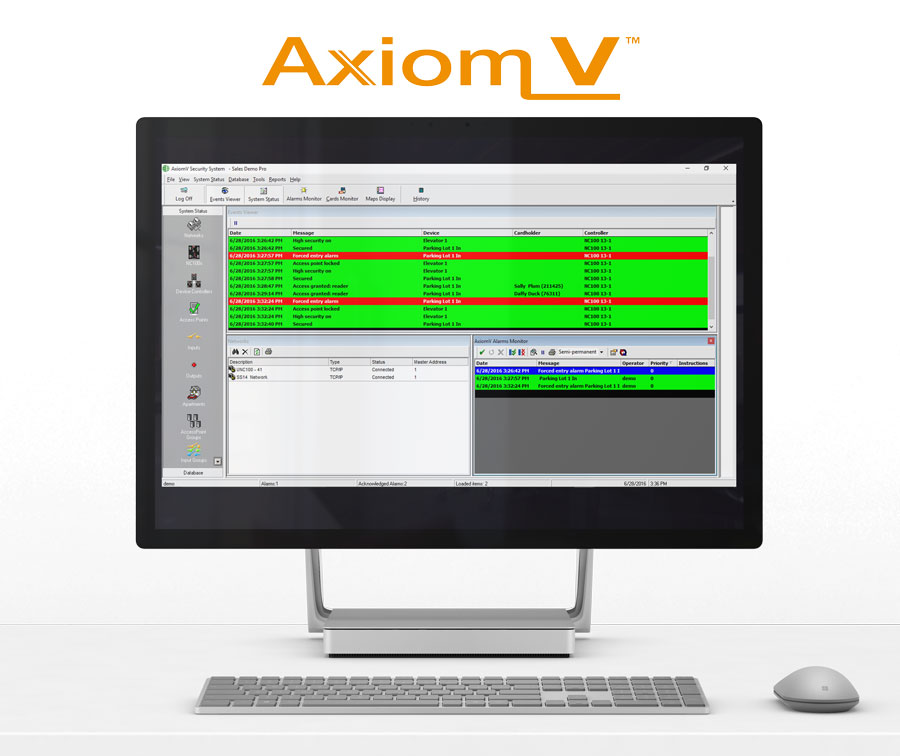
Bringing together different aspects of security management can be challenging. AxiomV stands up to the challenge by combining Access Control and Alarm Monitoring with Video, Building management automation, Asset tracking, Guard tour and Visitor management, and many more important security functions into an elegant and versatile security management solution.
Harnessing the power of the Microsoft SQL Server™and powerful MS .NET™ framework, AxiomV is positioned on the cutting edge of modern security technology. Adding new applications and solutions is easy due to the flexibility of the underlying software and hardware platform.
Solid architecture and a highly customizable, flexible user interface provides powerful tools for Enterprise Security management. Robust and highly sophisticated hardware implements a variety of flexible solutions at a firmware level. Designed and manufactured “in house”, AxiomV offers unmatched longevity and will insure a long life span for a security investment. AxiomV provides a sophisticated yet affordable solution for systems of all sizes.
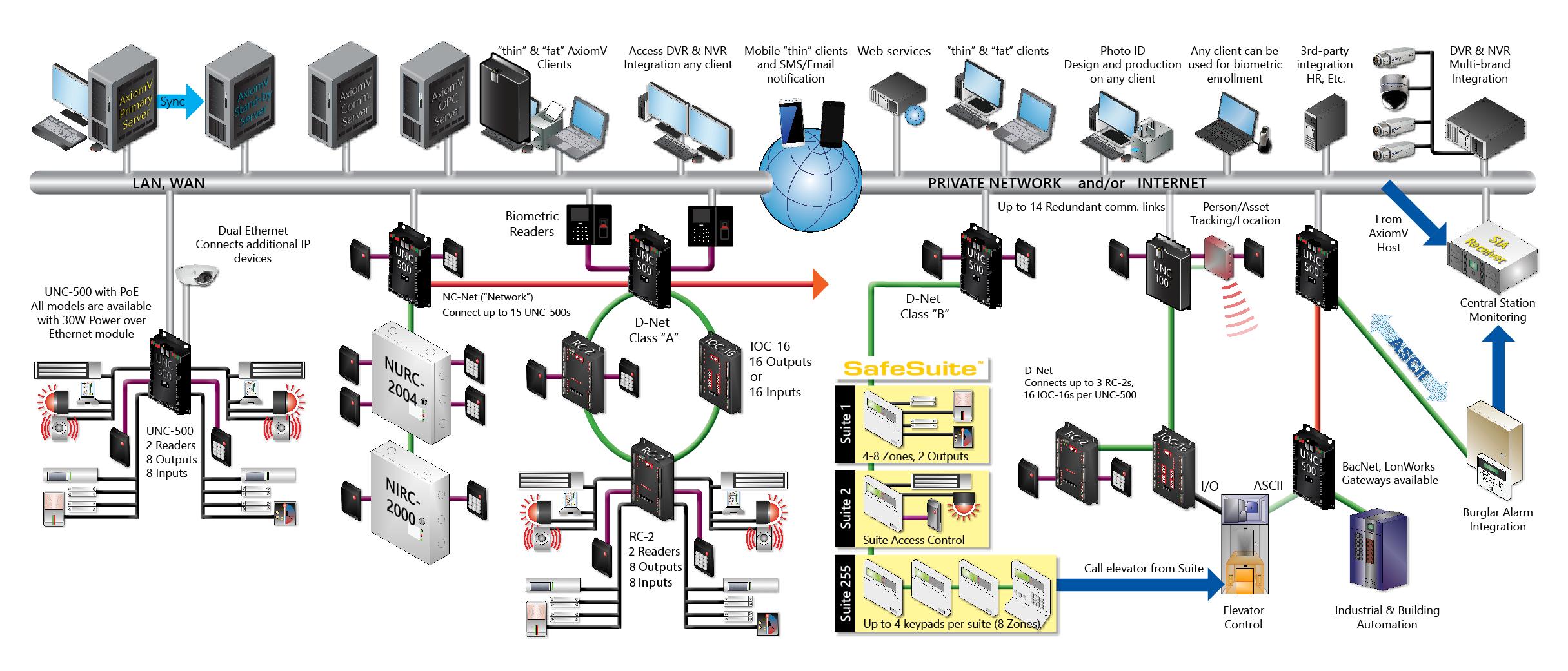
AxiomV™ Enterprise Edition is built on multi-server architecture, where discreet servers are implemented across the corporate network with “Hot standby” and automatic “Fail-over” features. In case of one of the communication and/or data servers going offline, there is a fully synchronized, up-to-date standby server ready to take over.
Each Communications Server handles multiple networks of UNC-500s / UNC-100s via a wide variety of communication technologies. Each one of those NC networks can have multiple connections to a Comm. Server. Our unique architecture allows these backup channels to connect to both “Master” and “Slave” UNCs/NCs constituting a network. This way, not only the loss of a communication channel is sustainable, but also a failure of one or more of the Network Controllers. The “Slave” controller will assume the role of a “Master” as the backup communications channel activates.
D-NET connects devices such as RC-2 Reader Controllers IOC-16 Input/Output controllers to the UNC-500 / UNC-100. 38.4 Kbps, RS- 485 circuit runs on a “Class A” bi-directional communication loop of twisted, shielded copper pair. UNC-500 / UNC-100, 4-8 of the RC- 2s and 16 IOC-16 controllers act as boosters and repeaters, combining the 3,000’ distances between individual devices into a 15,000’ loop. Due to its bi-directional nature, D-NET can sustain cable sabotage and failure of a device.
C-NET connects up to 15 UNC-500 / UNC-100s to each other creating a network of NCs. 2.5 Mbps, ARCNET packet-based, supervised and self-adjustable C-NET runs on a “Class A” bi-directional communication loop of twisted, shielded copper pair. Each UNC-100 acts as a booster and a repeater, combining 2,000’ distances between individual NCs into a 12,000’ loop. Due to its bi-directional nature, C-NET can sustain a C-NET cable sabotage and a failure of a UNC-500 / UNC-100.
Video Management
The Axiom system provides direct access to DVR features from the System Status screen, Event Log display, Interactive Maps, and History Report module

• History event viewing
• Live video on screen
• TCP/IP connections
• Report integration
• Pre, post event viewing
• Supports multiple makes
• Control PTZ on-screen
• Call/Shot assignment
Dynamic Mapping
Complete with manual or automatic display on alarm, mapping is enhanced by direct and full access to all control and configuration functionality, integration with live and event video for each device.

• Manual or auto display on alarm
• Direct Access to Control and Configure
• Integration with live event and video
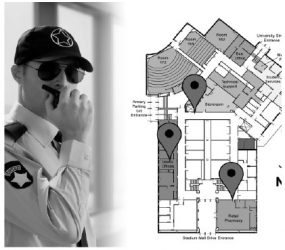
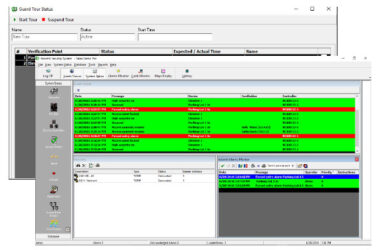
Interactive Guard Tour
To verify a door’s operation, presence of people in the area, or various other issues that can be out of normal order, a patrolling security officer is needed to make sure that these inspections are performed on time and in proper order
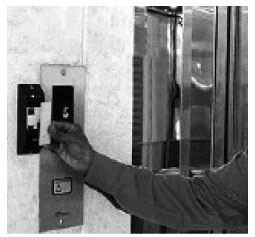
• Real-time operation
• Live progress display
• Uses existing readers at access points
• Start tours manually or by schedules
Integrated FUNCTIONS
Security Alarms
An extremely large number of unique alarm points can be monitored by an Axiom system. Each point can be fully configured for type of annunciation, priority, customizable action messages, ASCII output, CCTV trigger and executable links. Live graphic maps and color coded alarm handling instructions guide operators an efficient response to each alarm

Wireless Lock Support
As an accent to a hard wired solution or a total deployment of wireless lock technology Axiom interfaces with multiple brands of wireless locks simultaneously. This flexibility allows the right wireless lock to be used for the right application! Axiom provides complete monitoring of the wireless locks and all trouble conditions. Multiple modes of operation are offered depending on the wireless locks ability such as Dormitory and Privacy functions.
MULTIPLE FUNCTIONS

Browser and Mobile Support
Configuring the Web Server on the Axiom system will allow operators to control and administer the security system via a web browser from any operating system.
• Edit cards, schedules, access levels
• Monitor and control doors, alarm points and relay outputs
• Run database and activity reports
• Use any browser
Elevator Control
Axiom can communicate with elevator controller via programmable ASCII or input/output interface.
Architecture employed makes it easy to add visitor access functionality to existing systems. Permissions are easily configured in “Access Level” screen.
Visitor Management
Security requirements of large Organizations and facilities are always challenging, visitors must be screened, registered and signed in quickly in some cases with restricted access which is all possible using RBH’s Visitor Management System.

Features
• Faster throughput of visitors at reception
• Tablet based for security and front desk
• Online visitors reports
• For corporate/ residential / schools
• For multiple locations / units
• Manage and track visitors throughout facilities
Time and Attendance
The RBH Time and Attendance system provides improved efficiency, accuracy and productivity to the resource management and payroll process. This system has a roster management module built in that integrates with the time
and attendance, and access control hardware systems to help provide attendance, overtime, payroll and much more.
Features
Capable to integrate with any access control system
• Compatible with tablets and smart phones
• Email notification and active directory integration
• Late clock-in, early clock-out, and other exceptions list
• Employee and user role management